FindinFinindFinding Risks in Active Directory, VMware, Hyper-V, Azure, M365 and many more technologies supported by SecID Technology Risks Finder.
SecID Technology Risks Finder is built to enhance the security of key technologies like Microsoft Active Directory, VMware, Hyper-V, Azure, and Microsoft 365 tenants. It includes powerful query modules such as "Who Can", "Can a Single User", and "View". You can also create and run custom queries against your target environment. The output is a detailed report highlighting security issues and gaps. Once these gaps are identified, you can take corrective action to strengthen and secure your technology infrastructure.
For Active Directory, Technology Risks Finder offers below types of queries:
Who Can? Who can create, delete and modify and other operations.
Can a Single User? Can a single user take an action defined in the query operation.
View: Lets you view permissions and delegation defined. There are 40+ views supported for Active Directory.
"Who Can?" is a security query that identifies which users or groups have the ability to perform specific actions in Active Directory.
It analyzes ACLs on AD objects to find permissions like ResetPassword, WriteProperty, or GenericAll. This helps uncover misconfigurations that could lead to privilege escalation or lateral movement.
"Can a Single User?" is a targeted query that checks what actions a specific user can perform in Active Directory. It evaluates the user’s effective permissions across OUs, objects, and attributes. This includes rights like GenericAll, ResetPassword, CreateChild, or WriteProperty.It traces both direct rights and those gained through group membership or inherited permissions.
"View" queries are designed to provide visibility into the current configuration and security posture of Active Directory.
They show detailed information about objects like users, groups, OUs, GPOs, and their attributes. Unlike "Who Can" or "Can a Single User", these queries focus on what exists, not who can do what.
"Who Can?" is a type of query or analysis that answers the question:
"Who can perform a specific action on a specific object in Active Directory?"
It focuses on identifying users or groups who have abusable or sensitive permissions, whether directly or indirectly assigned.
| Query | Meaning | Risk if Abused |
|---|---|---|
| Who can reset passwords for Domain Admins? | Finds users who can reset passwords of privileged accounts. | Full domain compromise. |
| Who can replicate directory secrets? | Finds accounts with rights to replicate sensitive directory data (like Replicating Directory Changes). |
Credential dumping (e.g. DCSync attack). |
| Who can modify Group Policy Objects (GPOs)? | Identifies users who can edit GPOs applied to key OUs. | Privilege escalation via startup scripts or policy injection. |
| Who can create user accounts in a sensitive OU? | Reveals users with CreateChild rights. |
Creation of rogue users or backdoors. |
| Who can link GPOs to OUs? | Determines who can attach policies to OUs. | Unintended policies applied, leading to misconfigurations. |
| Who can modify servicePrincipalName (SPN)? | Checks for users who can write the SPN attribute. | Enables Kerberoasting attacks. |
"Can a Single User" is a type of query or analysis designed to answer the question:
"Can a specific user perform sensitive or potentially abusable actions in Active Directory?"
This analysis simulates the permissions of a single user (directly or through group membership, delegated rights, or inherited permissions) to identify whether that account poses a risk within the environment.
| Query | Meaning | Risk if Abused |
|---|---|---|
| Can user reset Domain Admin passwords? | Checks if the specified user can reset passwords of high-privilege accounts. | Full domain compromise. |
| Can user replicate directory secrets? | Determines if the user can perform DCSync-like actions to extract password hashes. | Credential theft and lateral movement. |
| Can user modify GPOs? | Verifies if the user can edit Group Policy Objects affecting privileged systems or users. | Privilege escalation or code execution. |
| Can user create accounts in sensitive OUs? | Evaluates whether the user can create objects in critical organizational units. | Creation of persistent access (backdoors). |
| Can user modify SPNs? | Checks if the user can change servicePrincipalName attributes. | Enables Kerberoasting for hash extraction. |
| Can user delete or disable accounts? | Identifies whether the user can remove or deactivate key identities. | Disruption of services or denial of access. |
| Can user escalate privileges? | Assesses if the user can indirectly gain higher privileges through object control. | Undetected privilege escalation path. |
SecID allows you to build custom Risk Finder Templates using your own queries. For example, you can include checks for who can create, delete, or modify specific object types, along with other permission-based queries.

SecID enables you to add high-priority security queries, allowing you to efficiently run targeted checks against your Active Directory environment. This helps in quickly identifying security risks such as excessive privileges, misconfigured permissions, dormant accounts, and potential compliance violations. By surfacing these issues proactively, SecID supports continuous security monitoring and helps strengthen your overall identity and access management posture.

quickly execute the query to find risks
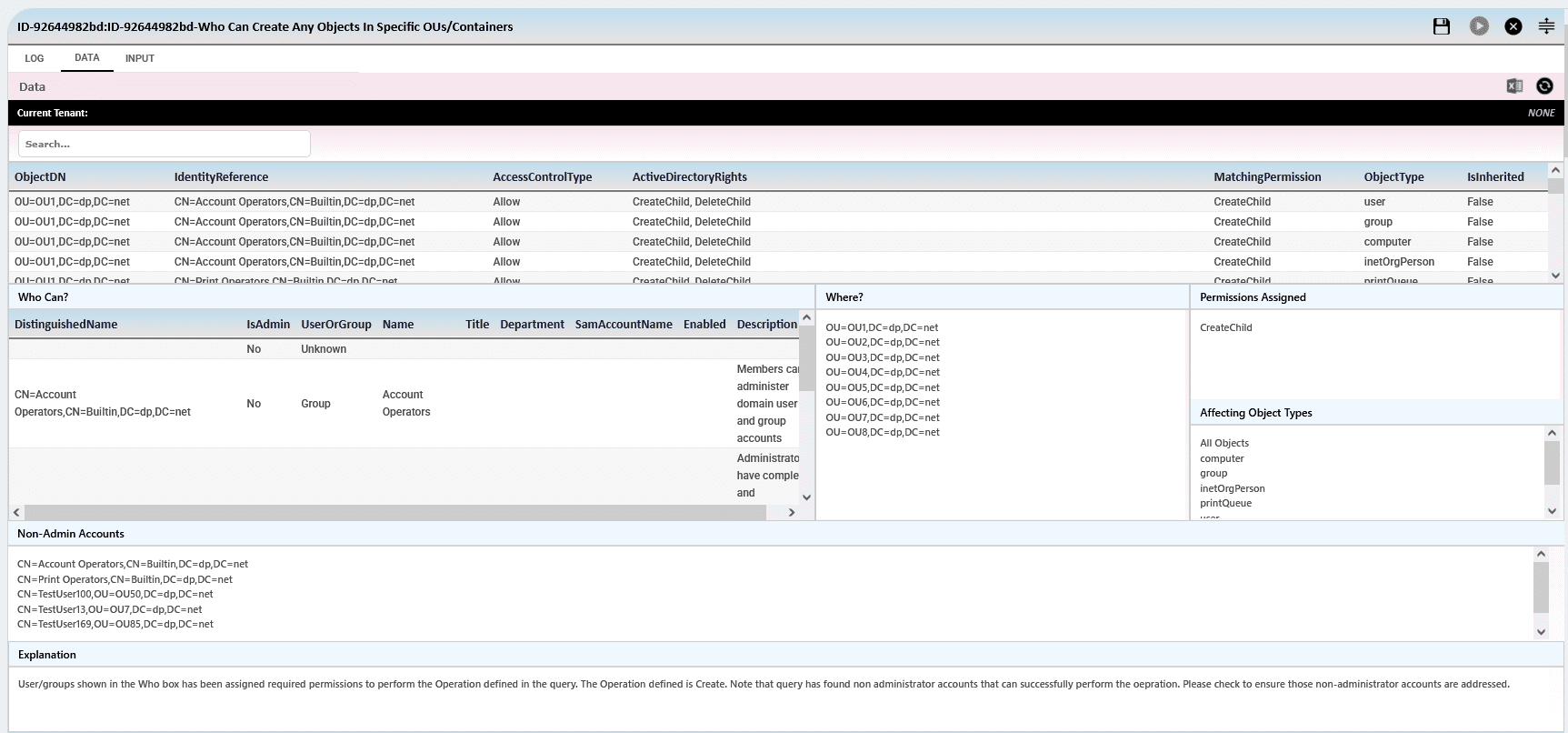
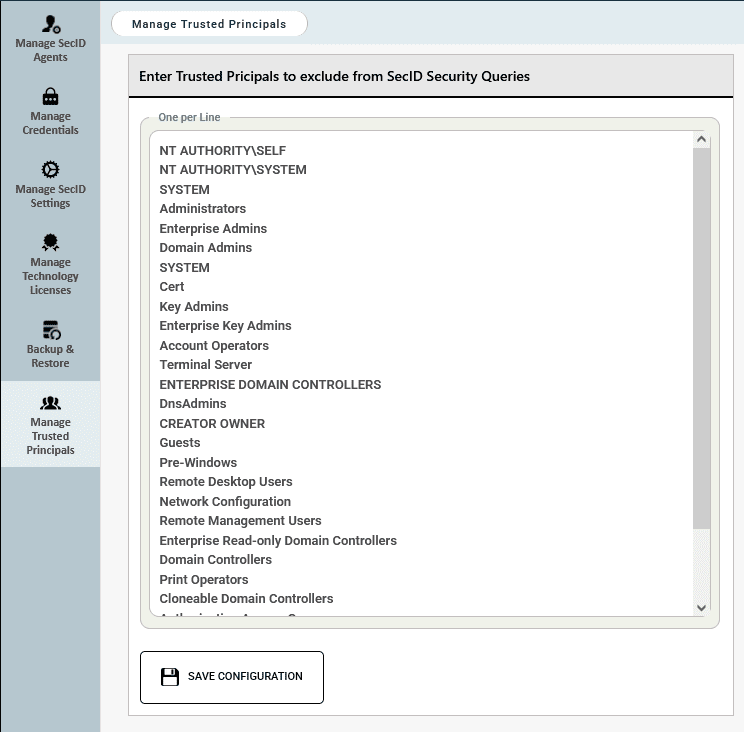
Trusted principals are user or group accounts that are considered reliable and may be granted specific permissions within Active Directory.
For example, you have defined a list of Trusted Principals and if SecID Technology Risks Finder identifies any users or groups that pose a potential risk due to their permissions in Active Directory and are NOT part of the Trusted Principals, you may want to review them. Trusted principals such as Domain Admins, Enterprise Admins, or any custom groups you consider safe should be excluded from the results to ensure the Risks Finder report remains focused and relevant.
We have defined a list of Trusted Principals to ensure they are excluded from the Risks Finder report. These default accounts are assigned standard permissions during Active Directory installation and can be safely added to the exclusion list.
Who Can Have Full Control On Any Objects In Active Directory
Who Can Have Full Control On users In Active Directory
Who Can Have Full Control On computers In Active Directory
Who Can Have Full Control On Security Groups In Active Directory
Who Can Have Full Control On Organizational Units In Active Directory
Who Can Have Full Control On Contacts In Active Directory
Who Can Have Full Control On Managed Service Accounts In Active Directory
Who Can Have Full Control On Group Managed Service Accounts In Active Directory
Who Can Have Full Control On Printers In Active Directory
Who Can Have Full Control On Network Shares In Active Directory
Who Can Have Full Control On Service Connection Points In Active Directory
Who Can Have Full Control On Container In Active Directory
Who Can Create Any Objects In Active Directory
Who Can Create users In Active Directory
Who Can Create computers In Active Directory
Who Can Create Security Groups In Active Directory
Who Can Create Organizational Units In Active Directory
Who Can Create Contacts In Active Directory
Who Can Create Managed Service Accounts In Active Directory
Who Can Create Group Managed Service Accounts In Active Directory
Who Can Create Printers In Active Directory
Who Can Create Network Shares In Active Directory
Who Can Create Service Connection Points In Active Directory
Who Can Create Container In Active Directory
Who Can Delete Any Objects In Active Directory
Who Can Delete users In Active Directory
Who Can Delete computers In Active Directory
Who Can Delete Security Groups In Active Directory
Who Can Delete Organizational Units In Active Directory
Who Can Delete Contacts In Active Directory
Who Can Delete Managed Service Accounts In Active Directory
Who Can Delete Group Managed Service Accounts In Active Directory
Who Can Delete Printers In Active Directory
Who Can Delete Network Shares In Active Directory
Who Can Delete Service Connection Points In Active Directory
Who Can Delete Container In Active Directory
Who Can Modify Any Objects In Active Directory
Who Can Modify users In Active Directory
Who Can Modify computers In Active Directory
Who Can Modify Security Groups In Active Directory
Who Can Modify Organizational Units In Active Directory
Who Can Modify Contacts In Active Directory
Who Can Modify Managed Service Accounts In Active Directory
Who Can Modify Group Managed Service Accounts In Active Directory
Who Can Modify Printers In Active Directory
Who Can Modify Network Shares In Active Directory
Who Can Modify Service Connection Points In Active Directory
Who Can Modify Container In Active Directory
Who Can Change Permissions Of Any Objects In Active Directory
Who Can Change Permissions Of users In Active Directory
Who Can Change Permissions Of computers In Active Directory
Who Can Change Permissions Of Security Groups In Active Directory
Who Can Change Permissions Of Organizational Units In Active Directory
Who Can Change Permissions Of Contacts In Active Directory
Who Can Change Permissions Of Managed Service Accounts In Active Directory
Who Can Change Permissions Of Group Managed Service Accounts In Active Directory
Who Can Change Permissions Of Printers In Active Directory
Who Can Change Permissions Of Network Shares In Active Directory
Who Can Change Permissions Of Service Connection Points In Active Directory
Who Can Change Permissions Of Single Object In Active Directory
Who Can Change Permissions Of Domain Admins Security Group In Active Directory
Who Can Change Permissions Of Enterprise Admins Security Group In Active Directory
Who Can Change Permissions Of Containers In Active Directory
Who Can Change Permissions Of AdminSDHolder In Active Directory
Who Can Reset Password Of Users In Active Directory
Who Can Reset Password Of Privileged Accounts In Active Directory
Who Can Manage FGPP – In Active Directory
Who Can Manage GPOs – In Active Directory
Who Can Delete GPOs – In Active Directory
Who Can Link/Unlink GPOs – In Active Directory
Who Can Modify Membership Of Security Groups In Active Directory
Who Can Take Ownership Of Users In Active Directory
Who Can Take Ownership Of Computers In Active Directory
Who Can Take Ownership Of Security Groups In Active Directory
Who Can Take Ownership Of Organizational Units In Active Directory
Who Can Take Ownership Of Group Policy Objects In Active Directory
Who Can Disable/Enable Users In Active Directory
Who Can Disable/Enable Computers In Active Directory
Who Can Reset Computers In Active Directory
Who Can Unlock Users In Active Directory
Who Can Modify-Expiration Date Of Users In Active Directory
Who Can Modify-Smart Card Requirements Of Users In Active Directory
Who Can Modify-Force Change Password At Next Logon Of Users In Active Directory
Who Can Modify-Profile Path Of Users In Active Directory
Who Can Modify-Logon Script Of Users In Active Directory
Who Can Modify-DES-Encryption Of Users In Active Directory
Who Can Modify-Sensitive and cannot be delegated Of Users In Active Directory
Who Can Modify-Kerberos Pre-Authentication Of Users In Active Directory
Who Can Modify-Password Of Users In Active Directory
Who Can Modify-Maximum Password Age Of Users In Active Directory
Who Can Modify-Minimum Password Age Of Users In Active Directory
Who Can Modify-Lockout Duration Of Users In Active Directory
Who Can Modify-Lockout Threshold Of Users In Active Directory
Who Can Modify-Lockout Observation Window Of Users In Active Directory
Who Can Replicate Secrets – In Active Directory
Here’s the list of frequently asked questions we have put together for SecID Technology Risks Finder. In case you still have any questions or require support on our products please feel free to connect with us using the contact us form or by sending an email to [email protected].
SecID Risks Finder for Active Directory requires a normal user account who has read permissions on the target objects. It doesn't need a Domain Admin or Enterprise Admin account to execute the queries.
It depends on the number of objects and query type. For example, if you need to check who can reset password of user accounts in Active Directory and if there are large number of user accounts then the execution may take some time to complete. We recommend that you build your own queries based on your requirements.
If you do not wish to show Default Principals such as Domain Admins, Enterprise Admins and other security principals that you have created then we recommend defining the Trusted Security Principals in the SecID Settings page.
SmartProfiler generates reports in Microsoft Word format. However, you can edit Impact and Recommendations for each test before generating the report.
ince report is generated in Microsoft Word format, you can brand these reports.
If you’re really looking for an Active Directory security assessment tool, download SmartProfiler and perform an assessment. This will assist you in identifying security, health, and configuration problems.
The health and misconfiguration assessment feature of SmartProfiler can be very useful in demonstrating that your environment does not use Microsoft’s suggested settings.
The best feature of SmartProfiler is that it can perform the assessment without a Global Admin account and without needing the registration of an Azure AD application. Because it only required a Global Reader Account, we were able to use the tool effectively for our clients and clients could allow us to conduct the assessment!
SmartProfiler's advanced assessment parameters really gives you insights about your Active Directory environment and make sure every risk is mitigated.
Copyright © DynamicPacks Technologies